New SEC Rules Prompt Closer Look at Cybersecurity

[Find the latest in trucking technology: Explore this quarter's issue of iTECH]
Trucking businesses will want to take a close look at the state of their cybersecurity in 2024 now that tough, new disclosure rules from the U.S. Securities and Exchange Commission have gone live.
Designed for public companies, the SEC crackdown on cybersecurity also has teeth for many private companies that do business with public firms.
The reason: The computer networks of private companies — including those of transportation providers — are often closely linked with those of their public company customers, according to Agnishwar Banerjee, product marketing manager at MetricStream, an IT advisory firm specializing in cyber risk management and compliance. That’s a big problem, given that hackers are well aware that if they can penetrate the loosely guarded computer network of a smaller, private company, they can often use that vulnerability to break into the computer system of a much larger, publicly traded partner, according to Banerjee.
For truckers, that reality is especially timely, given that transportation companies are no strangers to hacker break-ins.

Dysart
For example, less-than-truckload carrier Estes Express, which ranks No. 14 on the Transport Topics Top 100 list of the largest for-hire carriers in North America, was hit by a cyberattack in October, although it was able to recover quickly.
“The threat is large and increasing — quickly, exponentially,” said Wade Anderson, chief information officer and chief technology officer at Bay & Bay Transportation. “The data speaks for itself. The number of ransomware incidents and average payouts nearly doubled from 2022 to 2023. We all know the threat is big. But what is really concerning to me is the rate at which it is increasing in scope and scale.”
Jane Jazrawy, co-founder of driver training firm CarriersEdge, pointed to the shifting nature of cyberthreats.
“Hackers continue to evolve their tactics and try new approaches almost weekly,” she said. “Whether it’s probing for unpatched security holes, variations on phishing and ransomware or attempts to social engineer attacks through staff, the threat is ongoing and persistent.”
One of the major impacts businesses will see with the new SEC rules is that the cybersecurity plans of any public company — including their security arrangements with private trucking companies — are now public. That means anyone interested in closely scrutinizing the cybersecurity plan of any public company — including investors, an everyday citizen or an extremely curious journalist — can now pore over that company’s official report to the SEC to their heart’s content.
Gensler
“Whether a company loses a factory in a fire — or millions of files in a cybersecurity incident — it may be material to investors,” SEC Chair Gary Gensler said last summer in a statement on the new cybersecurity rules. “Currently, many public companies provide cybersecurity disclosure to investors. I think companies and investors alike, however, would benefit if this disclosure were made in a more consistent, comparable and decision-useful way.”
Besides mandating public disclosure, another new SEC requirement is a directive that forces businesses to report a known hack of their systems to the SEC within four days. That’s a far cry from the way many businesses have reported hacks previously. Often, victimized firms have been known to wait months before reporting a cyber intrusion. Others try to skirt reporting an incident altogether, hoping to avert bad press and liability.
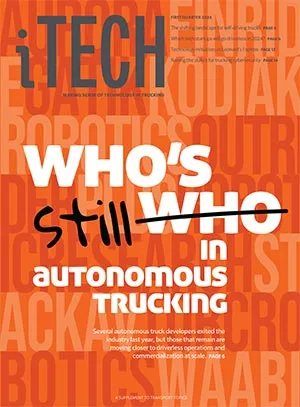
More Q1 iTECH
►Who's Still In Autonomous Trucking?
►Clevenger: Autonomous Trucking: A Rapidly Shifting Landscape
►Company snapshots: Aurora | Kodiak | Torc | Waabi | Stack AV | Gatik | Plus | Einride | Forterra | Outrider
►From November 2022: Who's Who in Self-Driving Truck Development
►Q and A: Chris DeMillo, Leonard's Express
►Dysart: New SEC Rules
Explore the Issue!
Meanwhile, other new SEC rules associated with the crackdown are designed to force companies to go into great, written detail about their cybersecurity infrastructure. Again, technically speaking, such reporting will only be required of publicly traded companies. But you can bet scores of computer security information officers at publicly traded companies will have nice, long talks during 2024 with many of their counterparts over at private companies regarding the strength of cybersecurity at those private firms.
As far as the specifics the SEC is mandating with its new rules, the agency now requires publicly traded companies to describe in detail the kinds of defenses they’ve developed to combat hackers, including the protections they’ve developed with third-party companies.
The SEC has decided to put corporate boards on the hook as well, requiring companies to describe in writing the oversight role the corporate board is playing in defending against hackers. Company management, too, is of course high up on the radar with new “in writing” requirements. The SEC also wants to know — in writing — if the company is working with assessors, consultants or auditors when it comes to cybersecurity planning. Finally, the SEC wants to see — also in writing — how companies have woven their hacker defense systems into their overall risk management system.
“These regulations will serve as an organized platform to learn from mistakes and ultimately prevent history from repeating itself,” said Daragh Mahon, executive vice president and chief information officer at truckload carrier Werner Enterprises. “The value of sharing learnings cannot be understated, as it enables the prevention of future missteps and the enhancement of overall security.”
Werner, based in Omaha, Neb., ranks No. 17 on the for-hire TT100.
Unsurprisingly, business reaction to the new SEC rules has been swift and decisive.
An October Deloitte & Touche poll, for example, found that 65% of public company executives have already made plans to toughen their defenses against hackers. Plus, more than half of executives surveyed vowed they would push third-party partners, including private companies, to beef up their cyber defenses as well.
New regulations aside, a good cybersecurity plan also just makes good business sense. That’s especially true given the never-ending cat-and-mouse game hackers insist on playing with businesses, year after year. A new survey from CompTIA, a training and certification organization for the computing industry, found that businesses, public and private, are still plagued by many of the usual suspects when it comes to cyber harassment.
In particular, malware remains a top concern at these organizations, with 40% of survey respondents identifying the malware scourge as a core focus of their defenses. Another 33% pointed to ransomware attacks as an area of focus, followed in priority by the hacking of firmware, Internet of Things attacks and attacks on computer hardware at 31% each.
COMTO's April Rai offers tips to increase workforce diversity and grow profits.. Tune in above or by going to RoadSigns.ttnews.com.
And, of course, our old friend, phishing — through which hackers attempt to penetrate business computer networks using stolen passwords, IDs, malicious links and similar methods — was also high on respondents’ lists, with 30% saying it’s a top priority.
Cyberthreats can affect company results on many fronts, both operational and financial, said Duwayne Powers, general manager of operations at trucking and logistics provider TLD Logistics Services.
“At my company, we’re continually evaluating the threat landscape and making adjustments as needed,” he said. “This year, we’ll be rolling out additional controls to ensure proper use of confidential information within an AI context. Also, additional processes and tools are being implemented to ensure administrative-level compliance to our IT systems.”
Paul Mohabir, director of information/system technology at Transervice Logistics, also emphasized the growing importance of cybersecurity in the transportation industry.
“The more technology advances, the more we have to be ready in case of any attack that can compromise our business, as we are in the service business, and any downtime interrupts our customers, who rely on us,” he said.
Transervice, headquartered in Lake Success, N.Y., ranks No. 97 on the for-hire TT100.
Fortunately, even the smallest trucking businesses can get up to speed on the latest tactics to combat hackers with a new cybersecurity program offered by American Trucking Associations and Serjon, a business consulting and IT security adviser firm.
Want more news? Listen to today's daily briefing above or go here for more info
The eight-session online course, available to members of ATA’s Technology & Maintenance Council, is designed to raise trucker awareness regarding “cyberthreats and risks, cybersecurity basics, firewalls and endpoint protection, equipment setup and configuration — and much more,” according to Urban Jonson, a cybersecurity specialist at Serjon.
Also featured in the sessions is a special focus on cybersecurity threats associated with common trucking technology tools, such as telematics systems and electronic logging devices, USB drives and Bluetooth.
Cyberattacks targeting the trucking industry continue to evolve at a rapid rate, according to the 2024 cybersecurity trends report recently issued by the National Motor Freight Traffic Association.
The report highlighted the prevalence of phishing scams, where hackers try to obtain sensitive information through fraudulent emails or messages. In some cases, hackers use that information to gain access to transportation companies’ enterprise systems and then launch ransomware attacks.
NMFTA also said it expects to see an uptick this year in a technique known as “vishing,” or voice phishing, where a scammer calls a person pretending to be a reputable business or coworker and requesting sensitive data.
Joe Dysart is an internet speaker and business consultant based in Manhattan. Voice: (631) 233-9770. Email: joe@customtechadvisor.com. Web: dysartnewsfeatures.com.





