Special to Transport Topics
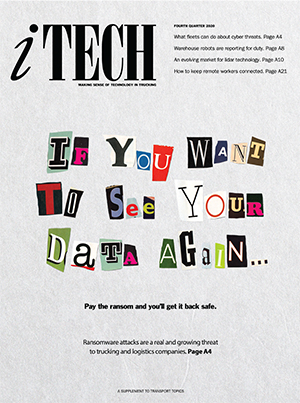
The Rising Threat of Ransomware: How Trucking Can Fend Off Cyberattacks

[Stay on top of transportation news: Get TTNews in your inbox.]
No fleet manager or logistics worker ever wants to experience the sinking feeling that comes with seeing a message flash on their computer screen revealing they have become the victim of a ransomware attack.
Internet and technology experts said ransomware breaches are becoming increasingly common and are not 100% preventable, but fleets and third-party logistics providers can take steps to reduce their risk and safeguard their businesses.
Ransomware attacks occur when hackers digitally break into a company’s IT infrastructure and encrypt — or lock up — selected files or the entire system. They then threaten to steal, delete or disseminate the company’s data unless they receive a ransom.
Partnering with proper software vendor companies is key. … But ultimately, the responsibility lies with the [fleet] or 3PL.
Chris DeMillo, director of systems development at Leonard’s Express
This form of cybercrime has become a top security threat for businesses of all sizes. Ransomware attacks are increasing precipitously, although the exact frequency can be difficult to quantify because some companies quietly pay the ransom without reporting an attack. During the first half of 2020, global reports of ransomware incidents across all industries skyrocketed 715% year-over-year, according to cybersecurity and antivirus software firm Bitdefender.
More Q4 iTECH stories
- The Rising Threat of Ransomware: How Trucking Can Fend Off Cyberattacks
- E-Smart Targets Better Tractor-Trailer Connectivity
- The Rise of the Warehouse Robot
- Trailer-Sharing Startup vHub Expands Marketplace
- Plus, FAW Self-Driving Truck Passes Certification Test in China
- Clevenger: Assembling the Autonomous Truck
- Spearin: Can On-Demand Freight Really Work for Trucking?
- Dysart: Curing Remote Workers’ Blues
Last year, transportation became one of the most cyberattacked industries in the United States. Ransomware attacks on fleets and 3PLs are especially insidious because they can compromise not just the victim’s information, but also that of clients and business partners. Even so, many transportation businesses still do not take the proper precautions against an attack or have a recovery plan in case one occurs.
The transportation management software that many trucking and logistics companies use to run their operations is designed to improve business efficiency, but is not intended to be a primary line of defense against ransomware. However, technology vendors do scrutinize cybersecurity protections when designing their software and can discuss appropriate security measures with their clients.
“Customers are trying to move freight and get more efficient, so cybersecurity is not in the forefront of their mindset. Helping them through the murky waters is part of our strategy. At the end of the day, it affects us all,” said Ben Barnes, chief security officer at McLeod Software.
“Partnering with proper software vendor companies is key. … But ultimately, the responsibility lies with the [fleet] or 3PL,” said Chris DeMillo, director of systems development at Leonard’s Express, a motor carrier and logistics provider based in Farmington, N.Y.
Once Bitten, Twice Shy
Cybersecurity and IT professionals say it is a well-known but unfortunate fact that a large proportion of companies do not put in place adequate prevention strategies, and they only take the risk seriously if they fall victim to a ransomware attack.

Elkins
“My experience is, regardless of industry — whether trucking or shipping or health care — once a company is hit with ransomware, they become far more serious about securing their data,” said William Elkins, chief technology officer at HudsonAnalytix. The maritime business risk management and cybersecurity company currently is working on trucking-centric solutions.
As threats continue to grow, more businesses are investing in cybersecurity insurance. Some fleets avoid this insurance because of the cost, which is rising as the number of ransomware attacks increases. Others purchase it and think their business then is adequately prepared, but that’s not enough, experts said.
“You really aren’t set and it can give you a false sense of security that it’s a panacea, when it’s not,” said Michael Riccio, chief marketing officer at Leonard’s Express. “What are you doing at the blocking and tackling level to alleviate having to use that insurance?”
The trucking and freight brokerage company was hit with a ransomware attack three years ago that it believes originated from an email phishing attempt, in which an internet user opens a fraudulent email that launches the ransomware.
The company did not pay the ransom and the hackers did not steal any data, but the situation was a red flag to step up its security protocols.
A lot of transportation companies may have underinvested in cybersecurity. Bay & Bay was no different. You take it for granted and think that it’s not going to happen to you.
Wade Anderson, Bay & Bay Transportation chief information officer
Eagan, Minn.-based trucking and logistics company Bay & Bay Transportation found itself in a similar situation two years ago when a ransomware attack locked up about 70% of its servers. It paid the ransom and then spent the following days working on recovery. The company used the incident as a catalyst to do better.
“A lot of transportation companies may have underinvested in cybersecurity. Bay & Bay was no different. You take it for granted and think that it’s not going to happen to you,” said Wade Anderson, the company’s chief information officer. “In trucking it is hard to make a dime… Everyone is fiscally concerned about investing too much effort or money into one thing, like cybersecurity. But that’s a risk.”
Small and medium-size transportation companies can be especially vulnerable because they sometimes assume attackers only target large businesses, and therefore they don’t invest in proper cybersecurity infrastructure. But a common ransomware tactic is for hackers to randomly send out a spam email blast that could reach thousands of businesses, regardless of size. Thus, preparation is key.
The universal mantra is that no single action is 100% foolproof in preventing attacks. Rather, a variety of measures collectively strengthen a transportation business’s infrastructure to make it less vulnerable and better able to bounce back after an incident.
An Ounce of Prevention
The first step is to devise a cybersecurity plan.
“[Although] having a plan doesn’t always help prevent it, if something happens… it lays out the playbook for how to deal with the problem,” McLeod’s Barnes said.

Barnes
The plan should include an assessment of the company’s most valuable assets, where in the system they live and entry points into the system.
“You’ve got to identify the crown jewels and figure out how to protect them,” Barnes said.
The asset inventory can help companies understand which preventive actions to consider. These could include installing firewalls, adding antivirus software or enlisting third-party cybersecurity services.
“When you’ve done this assessment, it’s a lot easier to put up a cyber budget. Offset that expense with the impact of an outage. You’ll make different decisions if you consider the cost,” said Elkins, of HudsonAnalytix.
Fleet managers might cringe at the thought of spending tens of thousands of dollars on cybersecurity infrastructure. But just one ransomware incident could easily cost more than that, not just in payment to hackers, but also with remediation and the potential loss of customers and proprietary information.
Plus, basic prevention doesn’t have to cost a lot.
“Companies can do this on a shoestring budget — even just creating a policy and training staff,” Bay & Bay’s Anderson said.
The plan also should identify integration points among technologies and documents. Transportation companies increasingly are adopting fleet and business management technology that is interconnected with many departments and operations, which means an attack on one asset could take down a company’s entire system.
Devising a cybersecurity plan should not just be the responsibility of the IT department. It needs input and buy-in from every department to be successful. All employees should be aware of their role in the plan.

Sandberg
“Make the plan ahead of time, print the plan, and have it all over the place,” said Chris Sandberg, vice president of information security at Trimble Transportation. “You should test every so often that the steps you have in place for the business haven’t changed and don’t need to be [updated] — at minimum annually, but preferably quarterly.”
Regular training is crucial, sources said. All employees should learn how to spot email phishing attempts, know not to click on attachments, create strong passwords, regularly change passwords and understand what to do about a message announcing a ransomware attack.
Phishing has become such a significant vulnerability point that spotting and avoiding these emails is now a leading ransomware prevention strategy. A training tactic gaining popularity is to run a phishing test every few weeks. Employees don’t know who will receive the faux email or when, but those who click on it might be asked to undergo additional training. System backups in a second location are a key element to prevent catastrophe in the event of a ransomware attack. IT departments should help decide whether cloud-based or offline backups are the best option for each fleet, but cloud options can have a big drawback.
“A lot of people have a backup, but it’s online and then the ransomware takes it down,” Trimble’s Sandberg said. “Offline backups are the best thing you can do to minimize an attack.”
Regularly updating computer operating systems and installing software patches also closes security gaps where intruders could gain entry.
Recovery and Restoration
If a ransomware attack occurs, fleets should enact the recovery steps in their plan to mitigate further damage and restore business functionality. That includes determining whether to pay the ransom, although cybersecurity experts largely advise against it.
Business operations usually are restored in chunks or phases over the course of hours or days, and IT workers must avoid reactivating the ransomware. The length of recovery time varies significantly depending on how much data the hackers encrypted, what protections already were in place and which restoration tools are immediately accessible.
How did turkey-to-table change this year? What obstacles were suppliers going through to get turkeys to grocery stores? Join us as we talk with J.J. Smith, President of Valley Proteins, about how staying open-minded and flexible helped his business of delivering turkeys persevere. Hear a snippet, above, and get the full program by going to RoadSigns.TTNews.com.
Recovery can be performed by an in-house IT team or by third-party services, depending on resource availability and finances. Some outside companies will even handle negotiating with hackers.
Regardless of who performs the restorative actions or whether a fleet decides to pay the ransom, experts recommend also contacting the FBI. The agency tracks and investigates ransomware attacks across all industries and works to apprehend and prosecute hackers.
In Bay & Bay’s situation, the FBI indicted two Iranian men for orchestrating the widespread SamSam ransomware attack.
“I spent more hours than I can count on the phone with the FBI,” Anderson said.
Although the initial inclination might be to keep quiet about an attack, contacting business partners and customers is advisable.
“You have an obligation in today’s world to let folks know you’ve had an incident,” Elkins said.
Some businesses, such as Bay & Bay and Leonard’s Express, have chosen to take this notification a step further by going public in the hope of sharing information that could prevent similar attacks from happening to others.
“We’ll do it even if we have a little egg on our face,” Anderson said.

Riccio
“We make mistakes. But I think if you can own up to your mistakes, people like a good comeback story,” Riccio said. “If we can help someone else thinking about this and avoid it happening to them, it’s only going to help the industry.”
Cybersecurity reporting tools also are available.
American Trucking Associations offers a service called Fleet CyWatch to help its motor carrier and council members report trucking-related cybercrimes and share prevention tips and information about the latest threats.
Still, getting fleets to open up about ransomware attacks remains a challenge. But working collaboratively to help identify cybersecurity trends, tactics and constructive guidance is possible without divulging proprietary information, experts said.
“If we don’t talk about what’s going on, it will just keep continuing,” McLeod’s Barnes said.
Want more news? Listen to today's daily briefing:
Subscribe: Apple Podcasts | Spotify | Amazon Alexa | Google Assistant | More







