Senior Reporter
Ex-Alabama Trooper Admits Hacking Into FMCSA Database

A former Alabama state trooper has pleaded guilty to hacking into the Federal Motor Carrier Safety Administration’s computer databases, gaining access to sensitive data using credentials he obtained while working for the Alabama Law Enforcement Agency, according to a one-count federal criminal charge of computer-related fraud announced March 19 by the U.S. Department of Transportation Inspector General.
The former trooper, Gary Scott Stratton, was listed as an employee of a transportation safety consulting company, identified in a criminal information court document only as “Company A.” He pleaded guilty to gaining unauthorized entry into DOT’s Computer Driver’s License Information System that contained records relating to holders of commercial driver licenses, according to his plea.
Stratton was an Alabama state trooper from 2010 to 2018 and also was a certified USDOT/FMCSA/CVSA certified Level I inspector from 2000 to 2018.
Although “Company A” was not identified in court documents, Transport Topics has learned that Stratton had been employed at Transportation Safety Services in Daphne, Ala., where the company’s website identified him as Scott Stratton, a DOT compliance expert. Stratton's presence on the website was removed on March 21.
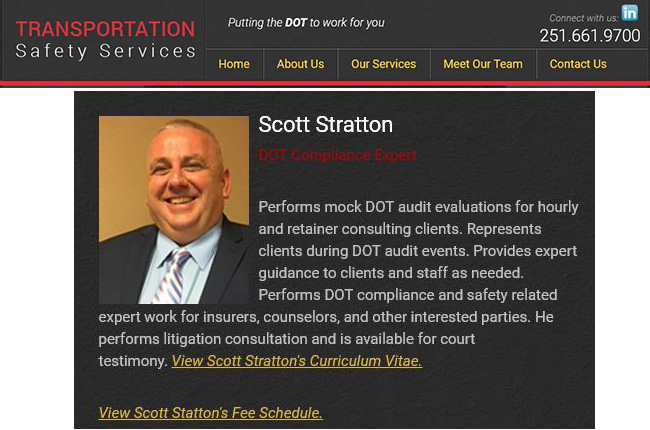
Portions of the Transportation Safety Services website, where former Alabama state trooper Gary Scott Stratton was listed prominently until March 21 as one of the company's experts.
TSS is a broad-based safety company with services ranging from representing clients during audits to safety rating upgrade plan development, according to the website. There have been no charges filed against the company.
Stratton’s curriculum vitae says he began working for TSS in June 2018. An administrative assistant at TSS said Stratton was not available for comment on March 19; the company’s president and owner, Lane VanIngen, did not return a phone message seeking comment. VanIngen worked for FMCSA as a motor carrier safety specialist from 1989 to 2002.

Skier
“I’d like your readers to know that Mr. Stratton does take public safety very seriously,” Stratton’s attorney, Andrew Skier of Montgomery, Ala., told TT. “Nothing that Mr. Stratton did placed anybody in danger.”
A spokesman for FMCSA said the agency does not comment on criminal investigations. A phone message left with the DOT IG was not returned.
Court documents said as an employee of Company A, it was Stratton’s job to assist long distance trucking company clients of Company A in complying with FMCSA regulations and passing FMCSA safety inspections, according to Stratton’s Feb. 5 plea agreement filed with a federal district court in Montgomery. Stratton is scheduled to be sentenced on June 12. His plea agreement said Stratton faces up to five years in prison, but noted that due to his cooperation he could receive a lesser sentence.
The information alleges that between June 22, 2018, and Jan. 17, 2019, Stratton intentionally accessed FMCSA databases without authorization “for financial gain and commercial advantage” as a “private consultant” with the unnamed company that provided motor carrier consulting services in Alabama.
Court documents did not reveal the extent of information Stratton might have obtained.
“When Stratton accessed the portal without authorization, he obtained information about upcoming FMCSA safety inspections of the clients of Company A. Stratton did so to gain a commercial advantage, in that he intended to share the information with the clients of Company A and therefore improve the commercial services provided by Company A to the clients,” the plea agreement said.
There have been past indications that information technology systems at FMCSA and the Department of Transportation have room for improvement in protecting what is known as “personal identifiable information” in their computer databases. A DOT Inspector General audit released in January 2018 recommended that the DOT chief privacy officer establish a continuous monitoring program for security controls to ensure that personal identifiable information systems remain compliant with the agency’s privacy risk management policy.
In a 2017 report on FMCSA’s information technology, the Government Accountability Office said the agency needed to strengthen its strategic planning and oversight to modernize its legacy technology systems, including the agency’s national medical examiners registry. In February, the DOT IG said it was beginning an audit of FMCSA’s medical certificate program due to a spike in truck-involved fatal crashes and fraudulent truck driver medical certification cases.
In December 2017, a hack into the FMCSA’s medical certification process caused a several-months-long shutdown of its national registered medical examiners site. Although the agency said no private data or sensitive personal information was stolen, the hack compelled a rebuild of the site that delayed the medical certification process for more than a year. The hack also caused a setback until June 2021 for the effective date of a final rule that would eliminate the need for truck drivers to carry a medical card as proof they passed their medical exams.




